reader comments
36 with 28 posters participating
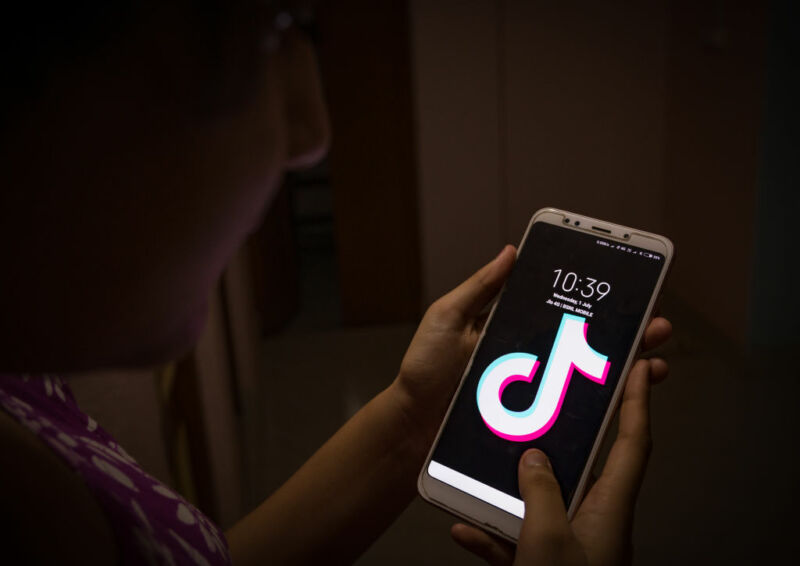
Microsoft said on Wednesday that it recently identified a vulnerability in TikTok’s Android app that could allow attackers to hijack accounts when users did nothing more than click on a single errant link. The software maker said it notified TikTok of the vulnerability in February and that the China-based social media company has since fixed the flaw, which is tracked as CVE-2022-28799.
The vulnerability resided in how the app verified what’s known as deeplinks, which are Android-specific hyperlinks for accessing individual components within a mobile app. Deeplinks must be declared in an app’s manifest for use outside of the app—so, for example, someone who clicks on a TikTok link in a browser has the content automatically opened in the TikTok app.
An app can also cryptographically declare the validity of a URL domain. TikTok on Android, for instance, declares the domain m.tiktok.com. Normally, the TikTok app will allow content from tiktok.com to be loaded into its WebView component but forbid WebView from loading content from other domains.
“The vulnerability allowed the app’s deeplink verification to be bypassed,” the researchers wrote. “Attackers could force the app to load an arbitrary URL to the app’s WebView, allowing the URL to then access the WebView’s attached JavaScript bridges and grant functionality to attackers.”
The researchers went on to create a proof-of-concept exploit that did just that. It involved sending a targeted TikTok user a malicious link that, when clicked, obtained the authentication tokens that TikTok servers require for users to prove ownership of their account. The PoC link also changed the targeted user’s profile bio to display the text “!! SECURITY BREACH !!”
“Once the attacker’s specially crafted malicious link is clicked by the targeted TikTok user, the attacker’s server, https://www.attacker[.]com/poc, is granted full access to the JavaScript bridge and can invoke any exposed functionality,” the researchers wrote. “The attacker’s server returns an HTML page containing JavaScript code to send video upload tokens back to the attacker as well as change the user’s profile biography.”
Microsoft said it has no evidence the vulnerability was actively exploited in the wild.