reader comments
139 with 89 posters participating
Mercenary spyware is one of the hardest threats to combat. It targets an infinitesimally small percentage of the world, making it statistically unlikely for most of us to ever see. And yet, because the sophisticated malware only selects the most influential individuals (think diplomats, political dissidents, and lawyers), it has a devastating effect that’s far out of proportion to the small number of people infected.
This puts device and software makers in a bind. How do you build something to protect what’s likely well below 1 percent of your user base against malware built by companies like NSO Group, maker of clickless exploits that instantly convert fully updated iOS and Android devices into sophisticated bugging devices.
No security snake oil here
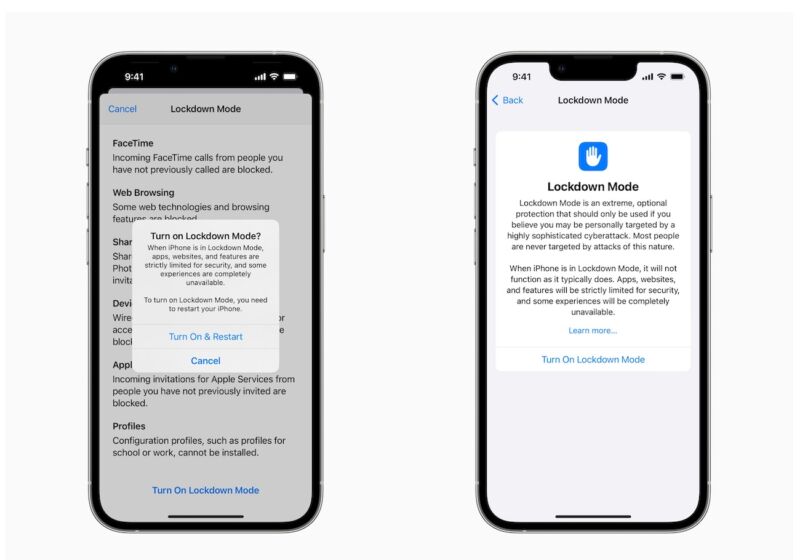
On Wednesday, Apple previewed an ingenious option it plans to add to its flagship OSes in the coming months to counter the mercenary spyware menace. The company is upfront—almost in your face—that Lockdown mode is an option that will degrade the user experience and is intended for only a small number of users.
“Lockdown Mode offers an extreme, optional level of security for the very few users who, because of who they are or what they do, may be personally targeted by some of the most sophisticated digital threats, such as those from NSO Group and other private companies developing state-sponsored mercenary spyware,” the company said. “Turning on Lockdown Mode in iOS 16, iPadOS 16, and macOS Ventura further hardens device defenses and strictly limits certain functionalities, sharply reducing the attack surface that potentially could be exploited by highly targeted mercenary spyware.”
As Apple says, Lockdown mode disables all kinds of protocols and services that run normally. Just-in-time JavaScript—an innovation that speeds performance by compiling code on the device during runtime—won’t run at all. That’s likely a defense against the use of JiT-spraying, a common technique used in malware exploitation. While in Lockdown mode devices also can’t enroll in what’s known as mobile device management used for installing special organization-specific software.
said Lockdown mode provides one of the first effective courses for vulnerable individuals to follow short of turning off their devices altogether.
“When you notify users that they’ve been targeted with sophisticated threats, they inevitably ask ‘How can I make my phone safer?” he wrote.’ “We haven’t had many great, honest answers that really make an impact. Hardening a consumer handset is really out of reach.”
3/There’s a common mental barrier among big platforms & OS developers around mainstreaming high-security features.
A lot of inevitable considerations, like:
– Worse user experience (esp. vs. the competition!)
– Breaking features
– More customer support resources required, etc.— John Scott-Railton (@jsrailton) July 6, 2022
Now that Apple has opened the door, it’s inevitable that Google will follow suit with its Android OS and it wouldn’t be surprising for other companies to also fall in line. It may also begin a useful discussion in the industry about broadening the approach. If Apple will allow users to disable unsolicited messages from unknown people, why can’t it provide an option to disable built-in microphone, camera, GPS, or cellular capabilities?
One thing everyone should know about Lockdown mode, at least as described on Wednesday by Apple, is that it doesn’t stop your device from connecting to cellular networks and broadcasting unique identifiers like IMEI and ICCID. That’s not a criticism, just a natural limitation. And trade-offs are a core part of security.
So if you’re like most people, you’re never going to need Lockdown mode. But it’s great that Apple will be offering it because it’s going to make all of us safer.