reader comments
42 with 35 posters participating
Microsoft late Thursday confirmed the existence of two critical vulnerabilities in its Exchange application that have already compromised multiple servers and pose a serious risk to an estimated 220,000 more around the world.
The currently unpatched security flaws have been under active exploit since early August, when Vietnam-based security firm GTSC discovered customer networks had been infected with malicious webshells and that the initial entry point was some sort of Exchange vulnerability. The mystery exploit looked almost identical to an Exchange zero-day from 2021 called ProxyShell, but the customers’ servers had all been patched against the vulnerability, which is tracked as CVE-2021-34473. Eventually, the researchers discovered the unknown hackers were exploiting a new Exchange vulnerability.
Webshells, backdoors, and fake sites
“After successfully mastering the exploit, we recorded attacks to collect information and create a foothold in the victim’s system,” the researchers wrote in a post published on Wednesday. “The attack team also used various techniques to create backdoors on the affected system and perform lateral movements to other servers in the system.”
On Thursday evening, Microsoft confirmed that the vulnerabilities were new and said it was scrambling to develop and release a patch. The new vulnerabilities are: CVE-2022-41040, a server-side request forgery vulnerability, and CVE-2022-41082, which allows remote code execution when PowerShell is accessible to the attacker.
“At this time, Microsoft is aware of limited targeted attacks using the two vulnerabilities to get into users’ systems,” members of the Microsoft Security Response Center team wrote. “In these attacks, CVE-2022-41040 can enable an authenticated attacker to remotely trigger CVE-2022-41082.” Team members stressed that successful attacks require valid credentials for at least one email user on the server.
The vulnerability affects on-premises Exchange servers and, strictly speaking, not Microsoft’s hosted Exchange service. The huge caveat is that many organizations using Microsoft’s cloud offering choose an option that uses a mix of on-premises and cloud hardware. These hybrid environments are as vulnerable as standalone on-premises ones.
China Chopper, a webshell commonly used by Chinese-speaking threat actors, including several advanced persistent threat groups known to be backed by the People’s Republic of China.
GTSC went on to say that the malware the threat actors eventually install emulates Microsoft’s Exchange Web Service. It also makes a connection to the IP address 137[.]184[.]67[.]33, which is hardcoded in the binary. Independent researcher Kevin Beaumont said the address hosts a fake website with only a single user with one minute of login time and has been active only since August.
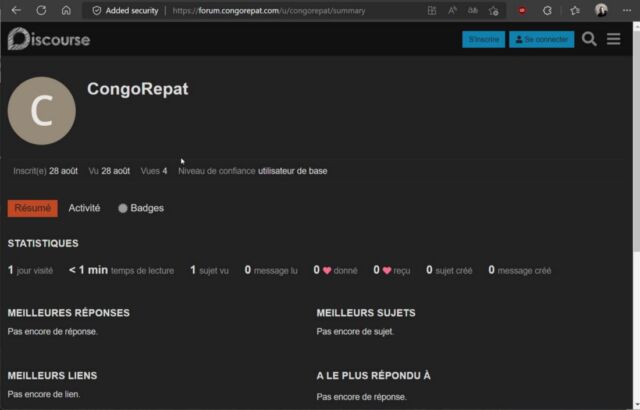
The malware then sends and receives data that’s encrypted with an RC4 encryption key that’s generated at runtime. Beaumont went on to say that the backdoor malware appears to be novel, meaning this is the first time it has been used in the wild.
People running on-premises Exchange servers should take immediate action. Specifically, they should apply a blocking rule that prevents servers from accepting known attack patterns. The rule can be applied by going to “IIS Manager -> Default Web Site -> URL Rewrite -> Actions.” For the time being, Microsoft also recommends people block HTTP port 5985 and HTTPS port 5986, which attackers need to exploit CVE-2022-41082.
Microsoft’s advisory contains a host of other suggestions for detecting infections and preventing exploits until a patch is available.