reader comments
33 with 25 posters participating
Amazon quietly but quickly patched a vulnerability in its Ring app that could have exposed users’ camera recordings and other data, according to security firm Checkmarx.
Checkmarx researchers write in a blog post that Ring’s Android app, downloaded more than 10 million times, made an activity available to all other applications on Android devices. Ring’s com.ring.nh.deeplink.DeepLinkActivity would execute any web content given to it, so long as the address included the text /better-neighborhoods/.
That alone would not have granted access to Ring data, but Checkmarx was able to use a cross-site scripting vulnerability in Ring’s internal browser to point it at an authorization token. Next, Checkmarx obtained a session cookie by authorizing that token and its hardware identifier at a Ring endpoint and then used Ring’s APIs to extract names, email addresses, phone numbers, Ring device data (including geolocation), and saved recordings.
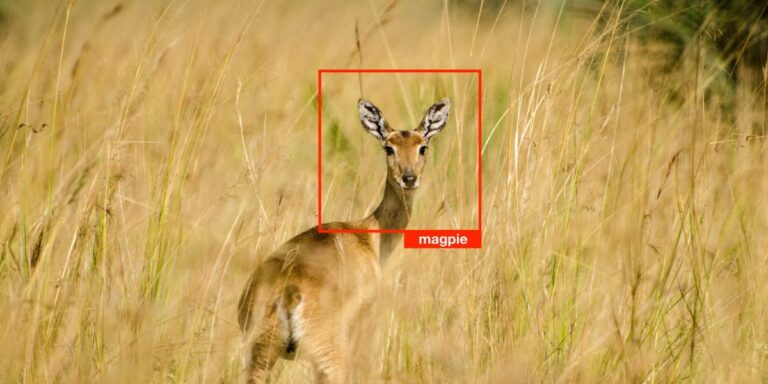
And then Checkmarx kept going. With access to its own example users’ recordings and any number of machine-learning-powered computer vision services (including Amazon’s own Rekognition), the security firm went wide-angle. You could, the firm found in its tests, scan for:
told The Record that taped-together vulnerabilities are coveted among hackers.
“Each would be problematic, but chaining them together, something hackers always try to do, made it so impactful.”
(Update 1:50 p.m. ET: Updated to correct spelling of Erez Yalon’s name. Ars regrets the error.)