
reader comments
31 with 24 posters participating
Researchers have unearthed a discovery that doesn’t occur all that often in the realm of malware: a mature, never-before-seen Linux backdoor that uses novel evasion techniques to conceal its presence on infected servers, in some cases even with a forensic investigation.
On Thursday, researchers from Intezer and The BlackBerry Threat Research & Intelligence Team said that the previously undetected backdoor combines high levels of access with the ability to scrub any sign of infection from the file system, system processes, and network traffic. Dubbed Symbiote, it targets financial institutions in Brazil and was first detected in November.
Researchers for Intezer and BlackBerry wrote:
What makes Symbiote different from other Linux malware that we usually come across, is that it needs to infect other running processes to inflict damage on infected machines. Instead of being a standalone executable file that is run to infect a machine, it is a shared object (SO) library that is loaded into all running processes using LD_PRELOAD (T1574.006), and parasitically infects the machine. Once it has infected all the running processes, it provides the threat actor with rootkit functionality, the ability to harvest credentials, and remote access capability.
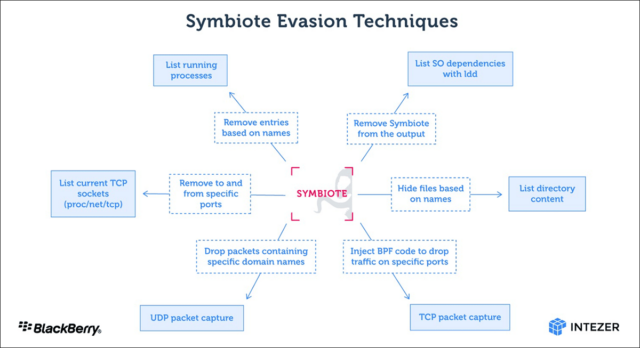
BPF in the image refers to the Berkeley Packet Filter, which allows people to conceal malicious network traffic on an infected machine.
“When an administrator starts any packet capture tool on the infected machine, BPF bytecode is injected into the kernel that defines which packets should be captured,” the researchers wrote. “In this process, Symbiote adds its bytecode first so it can filter out network traffic that it doesn’t want the packet-capturing software to see.”
One of the stealth techniques Symbiote uses is known as libc function hooking. But the malware also uses hooking in its role as a data-theft tool. “The credential harvesting is performed by hooking the libc read function,” the researchers wrote. “If an ssh or scp process is calling the function, it captures the credentials.”
So far, there’s no evidence of infections in the wild, only malware samples found online. It’s unlikely this malware is widely active at the moment, but with stealth this robust, how can we be sure?







