reader comments
34 with 25 posters participating
This story was originally published by ProPublica.
On February 25, the day after Russia invaded Ukraine, a prolific ransomware gang called Conti made a proclamation on its dark website. It was an unusually political statement for a cybercrime organization: Conti pledged its “full support of Russian government” and said it would use “all possible resources to strike back at the critical infrastructures” of Russia’s opponents.
Perhaps sensing that such a public alliance with the regime of Russian President Vladimir Putin could cause problems, Conti tempered its declaration later that day. “We do not ally with any government and we condemn the ongoing war,” it wrote in a follow-up statement that nonetheless vowed retaliation against the United States if it used cyberwarfare to target “any Russian-speaking region of the world.”
Conti was likely concerned about the specter of US sanctions, which Washington applies to people or countries threatening America’s security, foreign policy, or economy. But Conti’s attempt to resume its status as a stateless operation didn’t work out: Within days of Russia’s invasion, a researcher who would later tweet “Glory to Ukraine!” leaked 60,000 internal Conti messages on Twitter. The communications showed signs of connections between the gang and the FSB, a Russian intelligence agency, and included one suggesting a Conti boss “is in service of Pu.”
Yet even as Putin’s family and other Russian officials, oligarchs, banks, and businesses have faced an unprecedented wave of US sanctions designed to impose a crippling blow on the Russian economy, Conti was not hit with sanctions. Any time the US Treasury Department sanctions such an operation, Americans are legally barred from paying it ransom.
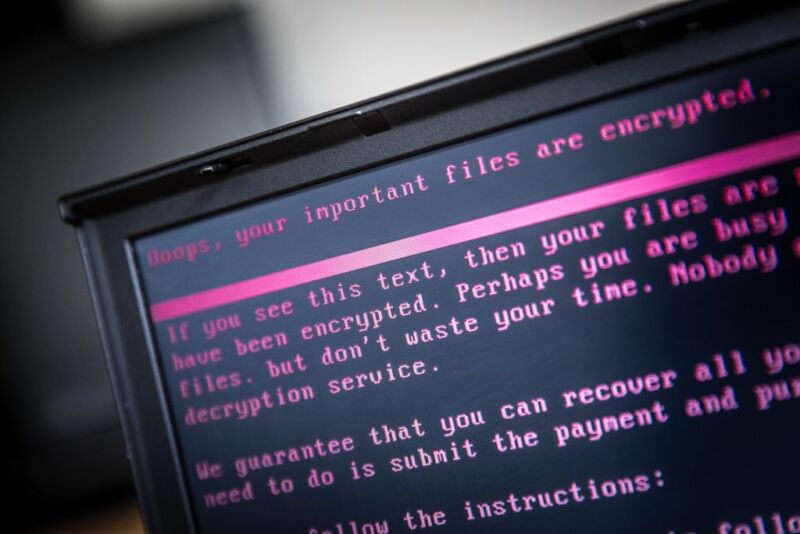
The fact that Conti wasn’t put on a sanctions list may seem surprising given the widespread damage it wrought. Conti penetrated the computer systems of more than 1,000 victims around the world, locked their files, and collected more than $150 million in ransoms to restore access. The group also stole victims’ data, published samples on a dark website, and threatened to publish more unless it was paid.
conference this year. (The Treasury Department did not respond to ProPublica’s requests for comment.)
Ransomware groups are constantly changing their names, in part to evade sanctions and law enforcement. Indeed, on Thursday, a tech site called BleepingComputer reported that Conti itself has “officially shut down their operation.” The article, which cited information from a threat-prevention company called AdvIntel, laid out details about the status of Conti’s sites and servers but was unambiguous on a key point: “Conti’s gone, but the operation lives on.”
The evanescence of the Conti name underscores another reason it’s hard to sanction ransomware groups: Putting a group on a list of sanctioned entities without also naming the individuals behind it or releasing other identifying characteristics could cause hardship for bystanders. For example, a bank customer with the last name “Conti” might pop up as a sanctioned person, creating unintended legal exposure for that person and the bank, said Michael Parker, a former official in OFAC’s Enforcement Division. The government then would have to untangle these snarls.