reader comments
30 with 17 posters participating, including story author
Hardware manufacturer Zyxel quietly released an update fixing a critical vulnerability that gives hackers the ability to control tens of thousands of firewall devices remotely.
The vulnerability, which allows remote command injection with no authentication required, carries a severity rating of 9.8 out of a possible 10. It’s easy to exploit by sending simple HTTP or HTTPS requests to affected devices. The requests allow hackers to send commands or open a web shell interface that enables hackers to maintain privileged access over time.
High-value, easy to weaponize, requires no authentication
The vulnerability affects a line of firewalls that offer a feature known as zero-touch provisioning. Zyxel markets the devices for use in small branch and corporate headquarter deployments. The devices perform VPN connectivity, SSL inspection, web filtering, intrusion protection, and email security and provide up to 5Gbps throughput through the firewall. The Shodan device search service shows more than 16,000 affected devices are exposed to the Internet.
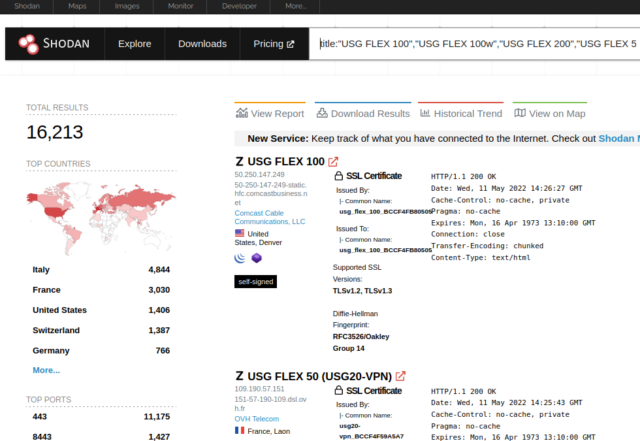
The specific devices affected are:
| Affected Model | Affected Firmware Version |
|---|---|
| USG FLEX 100, 100W, 200, 500, 700 | ZLD5.00 thru ZLD5.21 Patch 1 |
| USG20-VPN, USG20W-VPN | ZLD5.10 thru ZLD5.21 Patch 1 |
| ATP 100, 200, 500, 700, 800 | ZLD5.10 thru ZLD5.21 Patch 1 |
The vulnerability is tracked as CVE-2022-30525. Rapid7, the security firm that discovered it and privately reported it to Zyxel, said that the VPN series of the devices also supports ZTP, but they’re not vulnerable because they don’t include other required functionality. In an advisory published Thursday, Rapid7 researcher Jake Baines wrote:
here that automates the exploitation process.
Baines said that Rapid7 notified Zyxel of the vulnerability on April 13 and that the two parties agreed to provide a coordinated disclosure, including the fix, on June 21. The researcher went on to say that unbeknownst to Rapid7, the hardware manufacturer released a firmware update on April 28 that quietly fixed the vulnerability. Zyxel only obtained the CVE number on Tuesday, after Rapid7 asked about the silent patch, and published an advisory on Thursday.
According to AttackerKB, a resource on security vulnerabilities, CVE-2022-30525 is of high value to threat actors because it’s easy to weaponize, requires no authentication, and can be exploited in the default setup of vulnerable devices. Rapid7 representatives weren’t available to answer basic questions about the accuracy of that assessment.
Administrators must manually apply the patch unless they have changed default settings to allow automatic updating. Early indications are that the patch hasn’t been widely deployed, as a Shodan query for just one of the vulnerable firewalls, the ATP200, showed that only about 25 percent of exposed devices were running the latest firmware.
Vulnerabilities affecting firewalls can be especially severe because they sit at the outer edge of networks where incoming and outgoing traffic flows. Many firewalls can also read data before it’s encrypted. Administrators who oversee networks that use these affected devices should prioritize investigating their exposure to this vulnerability and patch accordingly.