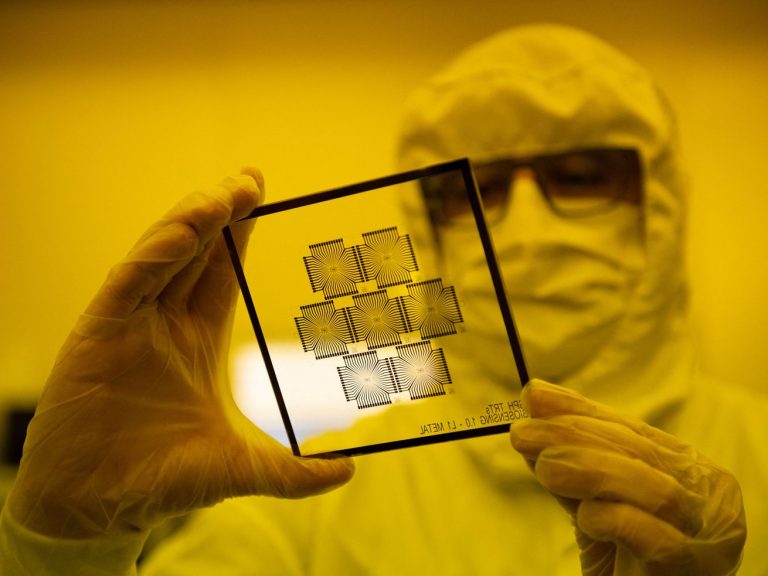
Enlarge (credit: Kevin Beaumont)
A compilation of screenshots posted online documents how some of the world’s most popular and trusted cloud-based services react when they are fed parameters used in the attack. To wit:
Read 7 remaining paragraphs | Comments