reader comments
0 with 0 posters participating
Microsoft on Thursday fingered Russia’s military intelligence arm as the likely culprit behind ransomware attacks last month that targeted Polish and Ukrainian transportation and logistics organizations.
If the assessment by members of the Microsoft Security Threat Intelligence Center (MSTIC) is correct, it could be cause for concern for the US government and its European counterparts. Poland is a member of NATO and a staunch supporter of Ukraine in its bid to stave off an unprovoked Russian invasion. The hacking group the software company linked to the cyberattacks—known as Sandworm in wider research circles and Iridium in Redmond, Washington—is one of the world’s most talented and destructive and is widely believed to be backed by Russia’s GRU military intelligence agency.
Sandworm has been definitively linked to the NotPetya wiper attacks of 2017, a global outbreak that a White House assessment said caused $10 billion in damages, making it the most costly hack in history. Sandworm has also been definitively tied to hacks on Ukraine’s power grid that caused widespread outages during the coldest months of 2016 and again in 2017.
Enter Prestige
Last month, Microsoft said that Poland and Ukraine transportation and logistics organizations had been the target of cyberattacks that used never-before-seen ransomware that announced itself as Prestige. The threat actors, Microsoft said, had already gained control over the victim networks. Then in a single hour on October 11, the hackers deployed Prestige across all its victims.
Once in place, the ransomware traversed all files on the infected computer’s system and encrypted the contents of files that ended in .txt, .png, gpg, and more than 200 other extensions. Prestige then appended the extension .enc to the existing extension of the file. Microsoft attributed the attack to an unknown threat group it dubbed DEV-0960.
On Thursday, Microsoft updated the report to say that based on forensic artifacts and overlaps in victimology, tradecraft, capabilities, and infrastructure, researchers determined DEV-0960 was very likely Iridium.

encoded PowerShell commands, and
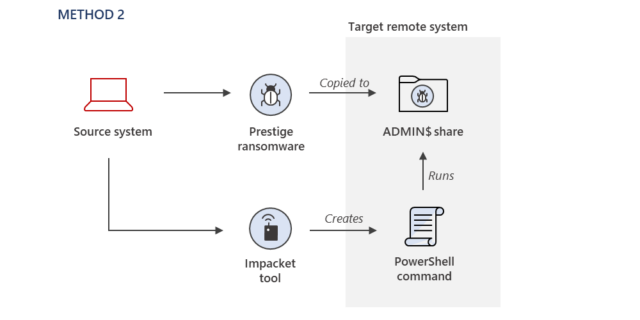
Default Domain Group Policy Objects
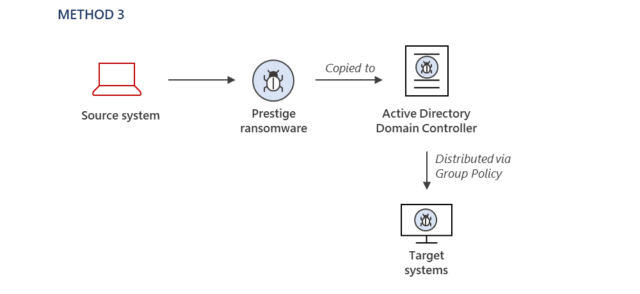
“Most ransomware operators develop a preferred set of tradecraft for their payload deployment and execution, and this tradecraft tends to be consistent across victims, unless a security configuration prevents their preferred method,” MSTIC members explained. “For this Iridium activity, the methods used to deploy the ransomware varied across the victim environments, but it does not appear to be due to security configurations preventing the attacker from using the same techniques. This is especially notable as the ransomware deployments all occurred within one hour.”
The post contains technical indicators that can help people figure out if they have been targeted.
Go to discussion…